Introduction
Ensuring the security of Cloud based environments has become more critical than ever before. With threat actors around the corner and ransomware attacks becoming more common each day it’s not a question if but when your organization is being the target.
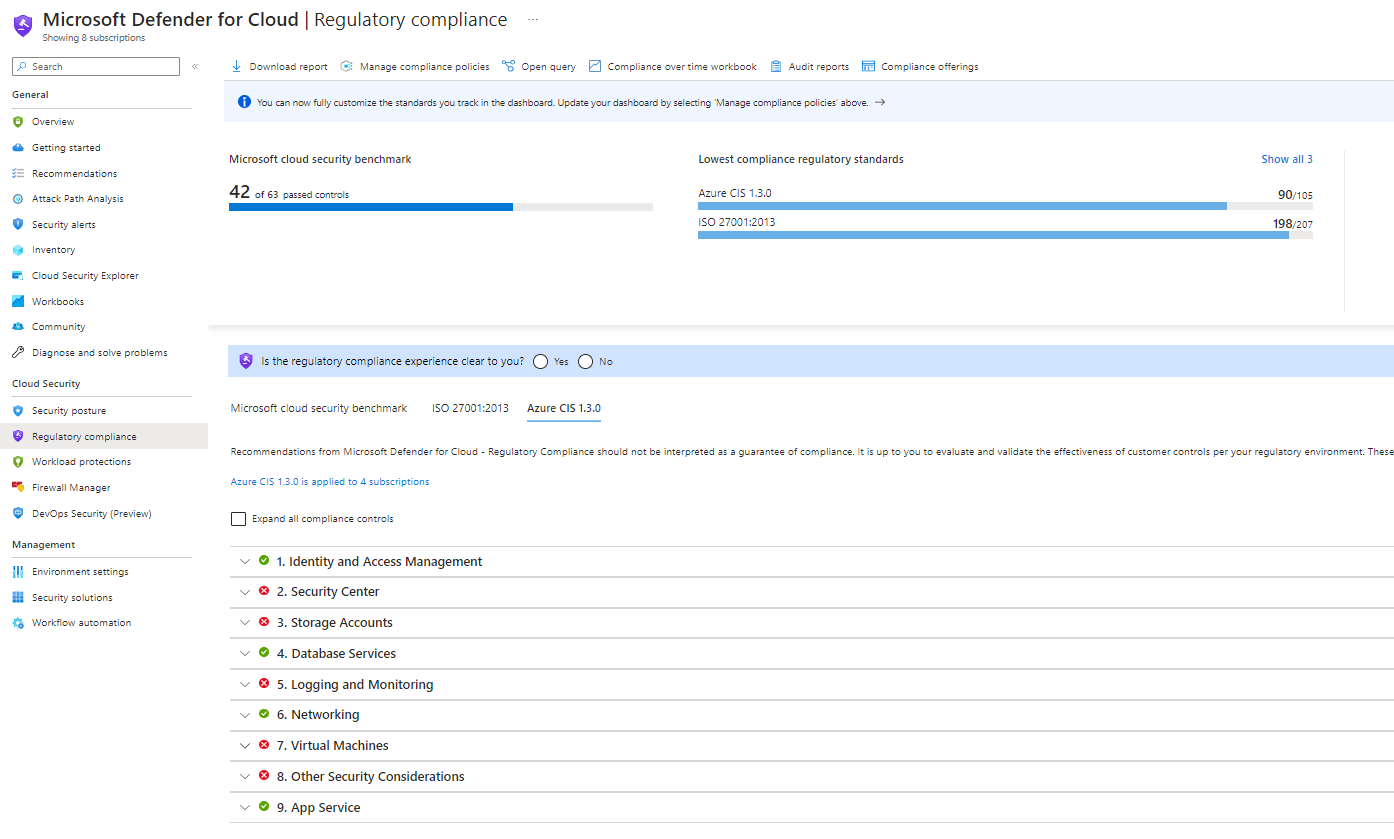
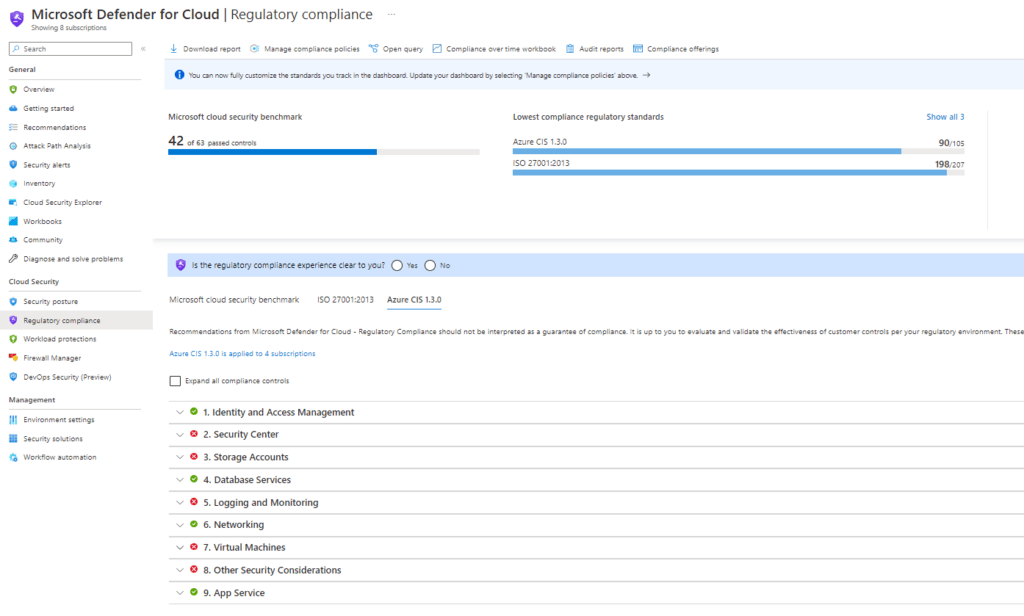
Defender for Cloud offers a wide set of build-in initiative policies like Azure CIS and ISO27001:2013 but it’s also possible to load in custom policies like BIO (Dutch Government Security Baseline) or NEN 7510 to match your security needs.
Understanding Initiatives in Defender for Cloud
Initiatives are a collection of security controls. They act as a set of guidelines to evaluate the security posture of Azure resources and provide recommendations for mitigating potential risks. It covers area’s such as Identity and Access Management, Network Security, Data Protection and more.
You can leverage this to remediate vulnerabilities and to create default policies to ensure Azure Resources are rolled out secure by default to ensure your secure score stays high.
You can monitor these controls within the regulatory compliance blade within Defender for Cloud which gives you an overview of non-compliant resources per policy and a general secure score.
It also offers the ability to exclude certain resources or scopes from a specific policy by creating temporary or permanent exempts or waivers.
So overall it’s a great tool to use within your organization to make sure your environment meets your compliance standards and to stay in control.
Deploying initiative policies
As stated before Microsoft has a lot of build-in policies you can implement based on your needs. To add those to your Regulatory Compliance
- Go to Azure Policy
- In the Policy Blade click on assignments
- On the top of the page there’s a button called ”Assign Initiatives”
- Choose a scope. You can assign the initiative policy as big or small as you want, from Management Groups to single resources.
- Within initiative definition you can assign one of the many built-in initiative policies.
- Decide on a name and description
- Choose a policy enforcement mode. Enforcement means resources not matching your policy will be denied during creation. If you disable this your policy will be in audit mode.
- After creation the initiative should show up in the Defender for Cloud regulatory compliance blade. It might take 24 hours before initial assessment is done.
Import a custom initiative policy.
Maybe I’ll write a blog about creating your own custom initiatives in a future blog. For now let’s focus on importing community build initiatives. Most controls you might need are available on Github so why build it yourself if someone already did it for you, right?
As an example we can take a look at BIO, the Dutch Government standard for information protection. Benjamin Tissink wrote a great initiative template which you can import with a single click. https://github.com/Azure/Bio-Compliancy
You can also look at initiatives more focused on Governance. Matthias Guentert published a great initiative set for naming conventions, which gives you a great kickstart setting up and enforcing your naming strategy. You can also replace it with your own naming convention, without having to rebuild complete templates.
https://github.com/matthiasguentert/azure-naming-convention-initiative