Collect logs
There’s multiple good reasons to enable logging for your Storage Accounts. One of them is to figure out if a Storage Account is still being accessed or to monitor connection sources. If you want access to this information you need to enable logging. If you don’t have a Log Analytics Workspace yet; create one.
The script below enables logging for all Storage Accounts in the target Subscription. If you only want to enable it for a single Resource you’re free to tweak it.
## Enable Storage Account logs to law for each account in a single subscription.
$storageAccounts = Get-AzStorageAccount
$WorkspaceId = "ResourceID" ## Resource ID of the Log Analytics Workspace
$DiagnosticSettingName = "Storage Logs"
Foreach ($StorageAccount in $storageAccounts) {
$ResourceId = $StorageAccount.Id
$metric = New-AzDiagnosticDetailSetting -Metric -RetentionEnabled -Category AllMetrics -Enabled
$setting = New-AzDiagnosticSetting -Name $DiagnosticSettingName -ResourceId $ResourceId -WorkspaceId $WorkspaceId -Setting $metric
Set-AzDiagnosticSetting -InputObject $setting
$metric = New-AzDiagnosticDetailSetting -Metric -RetentionEnabled -Category AllMetrics -Enabled
$readlog = New-AzDiagnosticDetailSetting -Log -RetentionEnabled -Category StorageRead -Enabled
$writelog = New-AzDiagnosticDetailSetting -Log -RetentionEnabled -Category StorageWrite -Enabled
$deletelog = New-AzDiagnosticDetailSetting -Log -RetentionEnabled -Category StorageDelete -Enabled
$Ids = @($ResourceId + "/blobServices/default"
$ResourceId + "/fileServices/default"
$ResourceId + "/queueServices/default"
$ResourceId + "/tableServices/default"
)
$Ids | ForEach-Object {
$setting = New-AzDiagnosticSetting -Name $DiagnosticSettingName -ResourceId $_ -WorkspaceId $WorkspaceId -Setting $metric,$readlog,$writelog,$deletelog
Set-AzDiagnosticSetting -InputObject $setting
}
}Read the logs
Open the Log Analytics Workspace that you used to store the logs and select Logs.
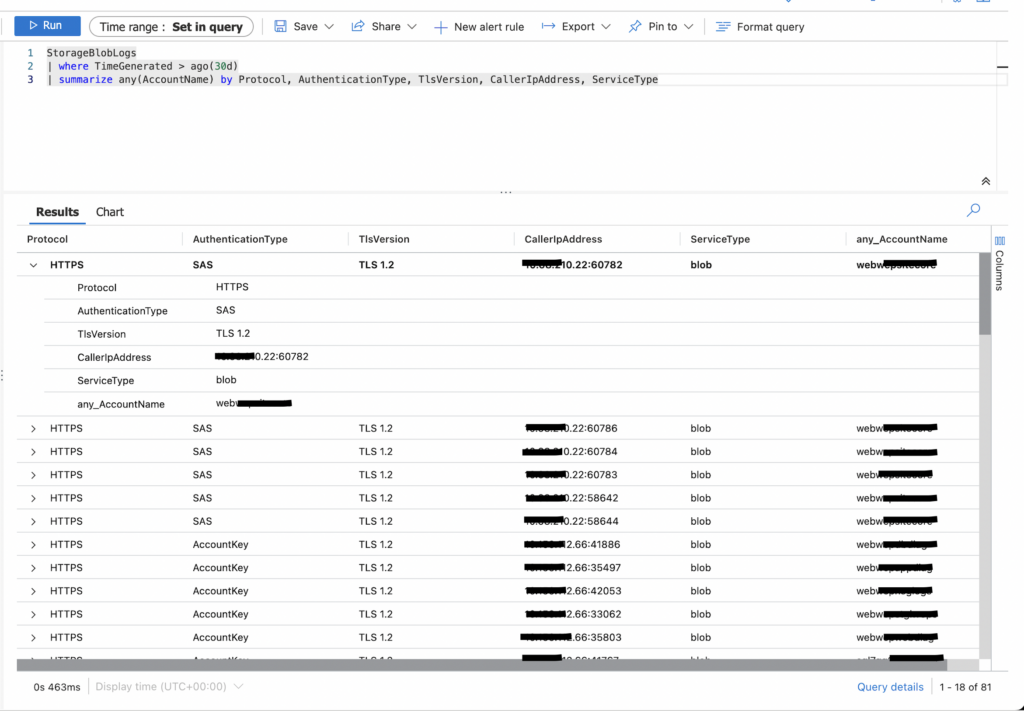
You can use KQL to collect data. I use the query in below example to monitor authentication methods and sources.
StorageBlobLogs | where TimeGenerated > ago(30d) | summarize any(AccountName) by Protocol, AuthenticationType, TlsVersion, CallerIpAddress, ServiceType
Result